
FIND OUT MORE
Managed SOC
Comprehensive cyber security coverage in a single package.

What Is A Managed SOC?
Managed Security Operations Centres combine different cyber solutions to provide a single service of comprehensive cybersecurity coverage. Our UK-Based SOC analysts use an AI-powered foundation to monitor your environment, gaining a dynamic, noise-free view of your threat landscape. Our approach leverages Artificial Intelligence (AI) and Machine Learning (ML) tools to automate threat prioritisation and rapidly surface sophisticated anomalies. This enables our team to efficiently identify, investigate, and mitigate any real-time attacks ensuring that your data, assets, and devices remain secure.
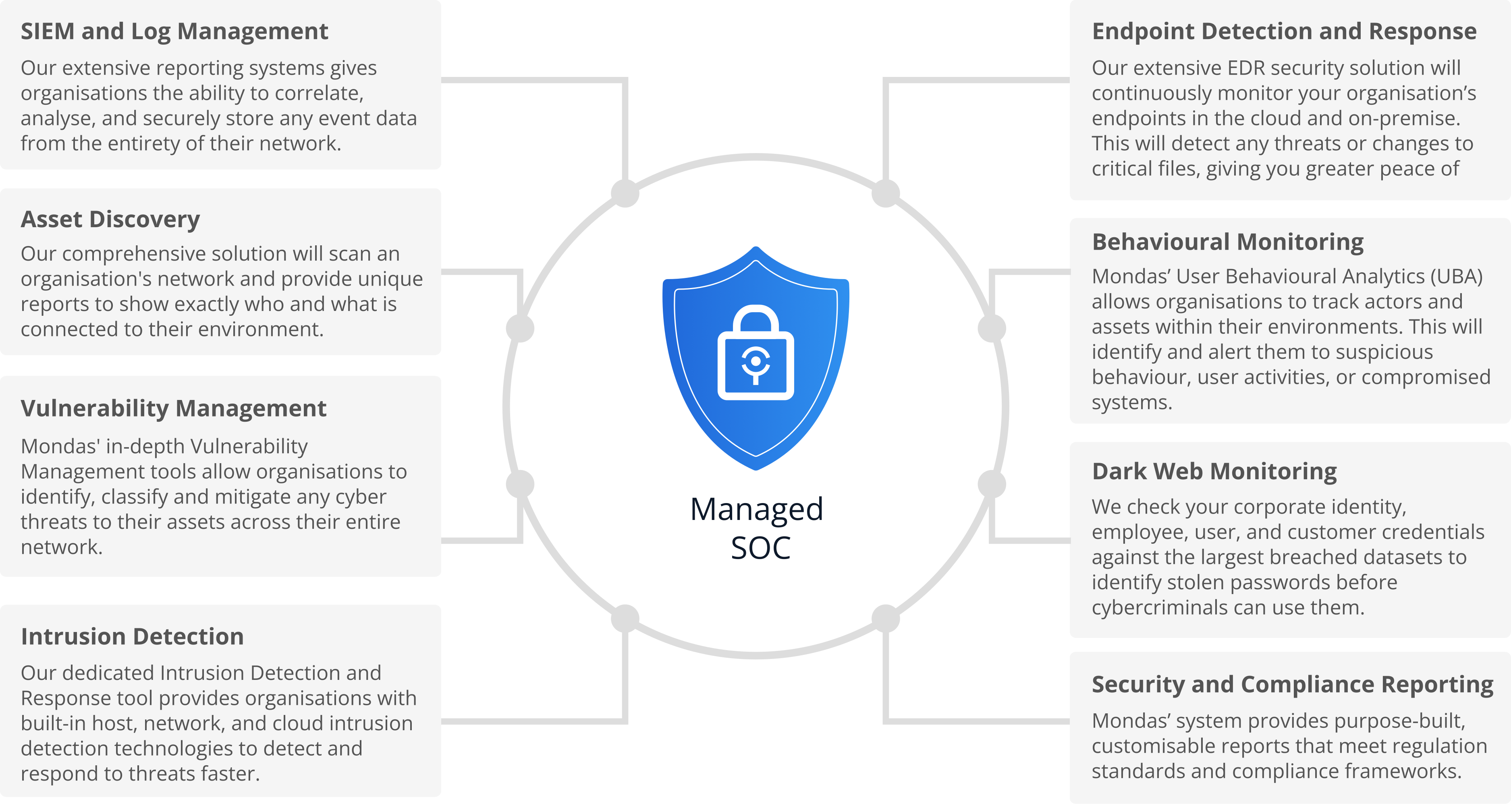
Our Service
SIEM and Log Management
Our extensive reporting systems gives organisations the ability to correlate, analyse, and securely store any event data from the entirety of their network.
Asset Discovery
Our comprehensive solution will scan an organisation’s network and provide unique reports to show exactly who and what is connected to their environment.
Vulnerability Management
Mondas’ in-depth Vulnerability Management tools allow organisations to identify, classify and mitigate any cyber threats to their assets across their entire network.
Intrusion Detection
Our dedicated Intrusion Detection and Response tool provides organisations with built-in host, network, and cloud intrusion detection technologies to detect and respond to threats faster.
Endpoint Detection and Response
Our extensive EDR security solution will continuously monitor your organisation’s endpoints in the cloud and on-premise. This will detect any threats or changes to critical files, giving you greater peace of mind.
Behavioural Monitoring
Mondas’ User Behavioural Analytics (UBA) allows organisations to track actors and assets within their environments. This will identify and alert them to suspicious behaviour, user activities, or compromised systems.
Dark Web Monitoring
We check your corporate identity, employee, user, and customer credentials against the largest breached datasets to identify stolen passwords before cybercriminals can use them.
Security and Compliance Reporting
Mondas’ system provides purpose-built, customisable reports that meet regulation standards and compliance frameworks.
Our UK-Based Managed SOC service combines our most popular managed services into a single package to provide comprehensive cyber security coverage at a very attractive price.

Start your FREE trial
Combine our most popular managed services into a single package with a 4 week free trial.
Start your Free TrialHow Our Managed SOC Works
Our SOC team supports operations throughout the entire incident response lifecycle. Before undergoing remediation, the threat must first be detected, investigated, and responded to. Our analysts are then well placed to remediate these threats.
Once an alarm is detected, our SOC team will follow agreed-upon playbooks to remediate and contain the threat. This may be to isolate a machine from the network or roll back systems to a safe state at any time of the day or night. No input is necessary from our customers, and a follow-up report summarising the incident will be sent.
Our Managed SOC leverages AI to perform continuous pre-filtering and analysis of security data. This accelerates the detection and prioritisation process so our dedicated analysts can take swift action to investigate, confirm, respond and remediate in real time.

Tap to enlarge

Book a free demo…
Book in a technical demo with one of our experts to understand how our cyber tools can help you tighten your security controls.
BOOK YOUR DEMOKey Benefits of a Managed SOC
Our Managed SOC service provides many benefits to our clients:
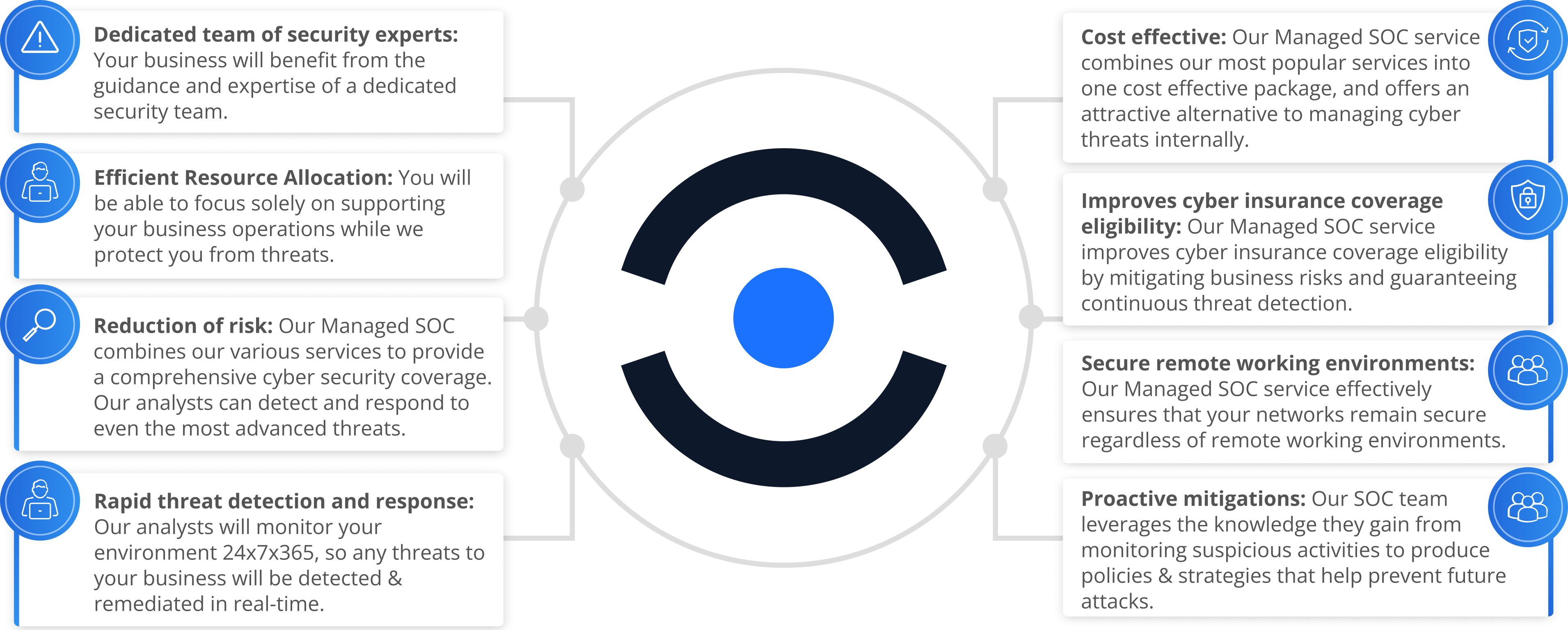
Dedicated team of security experts: Your business will benefit from the guidance and expertise of a dedicated security team.
Efficient Resource Allocation: You will be able to focus solely on supporting your business operations while we protect you from threats.
Reduction of risk: Our Managed SOC combines our various services to provide a comprehensive cyber security coverage. Our analysts can detect and respond to even the most advanced threats.
Rapid threat detection and response: Our analysts will monitor your environment 24x7x365, so any threats to your business will be detected and remediated in real-time.
Cost effective: Our UK-Based Managed SOC service combines our most popular services into one cost effective package, and offers an attractive alternative to managing cyber threats internally.
Improves cyber insurance coverage eligibility: Our Managed SOC service improves cyber insurance coverage eligibility by mitigating business risks and guaranteeing continuous threat detection.
Secure remote working environments: Our Managed SOC service effectively ensures that your networks remain secure regardless of remote working environments.
Proactive mitigations: Our SOC team leverages the knowledge they gain from monitoring suspicious activities to produce policies and strategies that help prevent future attacks.
Why You Should Choose Mondas…


Fully UK Based
Mondas Consulting is fully UK based. This means that throughout the operation of our services, none of your data will leave the UK, or be accessed by anyone outside of the UK. This gives you greater assurance in our services, and aligns with common business cybersecurity standards.


Security Vetted
All of our analysts have been security vetted. This means they have been subject to a thorough screening process and passed the relevant security checks before being cleared to handle your data. Accordingly, you can be confident that our team will pose no further risks to your business whilst delivering outstanding service.


Tailored Solutions
Our SOC services are fully adapted to the needs of each client. Each business boasts an entirely unique portfolio of assets that need protecting, which means our security experts must offer a specifically tailored service to safeguard these. We will assign a dedicated team of experts to your business, ensuring that our personnel understand your business and how to protect it best.


Skilled Staff
Regulating a business’ threat landscape requires highly skilled cybersecurity experts. Our Managed SOC tools are powered by AI to handle the massive volume of data, automate repetitive tasks, and filter out the noise, but it’s our certified security analysts who comprise the core of our service. They deliver detection, investigation, and remediation, providing the essential context, judgment, and strategic decision-making that no automation can replace. This combination of AI-driven efficiency and team expertise ensures you are protected from even the most sophisticated threats.


24/7/365 Monitoring
Our SOC analysts will monitor your security around the clock so you don’t have to. Any threats facing your business will be detected and managed in real-time. Accordingly, every threat will be reviewed, responded to, and documented instantaneously, regardless of the time.


Cost Effective
Mondas is committed to providing advanced threat protection at a price point that works for all businesses. This means we will tailor our SOC package to align with your budgetary constraints without compromising; we provide protection using expert analysts and leading technology in every engagement.


Bespoke Reporting
Our team will produce regular reports to ensure you are fully informed about the threats our analysts are protecting your business against and the measures they take to do this. This means you will have complete and unwavering visibility into the processes and protections we provide.

Like what you’re hearing?
Speak to an expert today on 01252 494 020 or…Email UsVisit Our LinkedIn
SPEAK TO USDownload our brochure
Take a look through our free brochure to understand how Mondas can help you reach your Cyber Security goals.


Download our brochure
Take a look through our free brochure to understand how Mondas can help you reach your Cyber Security goals.
Let’s get the ball rolling…
Mondas is here and ready to help. Fill out the form to let us know what we can do for you, and one of our experts will contact you.